You may think you have sufficient protection for your website but think again. People who indulge in cybercrime are always ready and monitor every moment waiting for a single loophole. Any such drawbacks or loophole will make it easier for them to enter and gain control over your website. Now, what happens after that depends on the hacker. They may demand ransom or even commit heinous crimes using your site.
However, you must protect your data as well as your website from any such attacks. And therefore, you must resort to prior precautions. But, unfortunately, if your website hacked because it lacks the initial protection, you must follow the ways that will assist you in retrieving it.
What Does Website Hacking Mean?
To discuss this, let me guide you from the very beginning. Earlier, programmers employed this word as a title to those who possess excellent skills in programming. Gradually, the hackers, with time, grew somewhat negative and during the mid-90s they started becoming malignant.
Nowadays, hackers develop their skills with technological advancements. However, there exists no doubt about their craft but that sure affects the protection of one’s privacy. And you, obviously, do not want any such phishing scams on your website. Hence, protect your site by keeping such attacks out. I present you how.
What to Do When Your Website is Hacked
First and foremost, you must not panic. Only then can you proceed with the steps to fix and retrieve the lost website of yours. Since the hackers have efficient ways to exploit the loopholes, you must be wise enough in battling them. You must indulge in self-research and then seek online sources for help.
There are multiple online experts that can assist you entirely. However, to retrieve your hacked website, you must perform the underlying steps carefully. Some may be a bit complex but doable.
Disinfect the Website
You must take your site offline. Turn your website off and quarantine it unless you diagnose and identify the problem. Mark your webpage’s entries of DNS to a static page that too on a separate server which employs a 503 HTTP responsive code.
I suggest this step just so that you can finish with the administrative tasks initially without potential hindrances. Users or visitors attempting to hack into or gain access to your website don’t encounter any bad code or even spam files. And this abstains the visitors from transmitting any malware too. However, if you do not know the process by which you can turn your website off, make sure that the third-party host does the job for you. Also, let your hosting service provider know that you plan to take it Offline.
But, you must be wary about the solutions. Some solutions are, in reality, not much of a help but they appear productive. Even if you revert your site back to a 4xx or 5xx HTTP status code, this won’t be sufficient to protect and shield your users.
And instead of that, the 503 status is a productive signal indicating that your website is temporarily down. But, you must receive the response from outside your hacked website or server.
Also, you must examine your website’s user account since hackers concentrate there as well. Hackers tend to make a new account. And in that case, you must take down the account names and delete. Also, ensure to keep them on record which serves as an important clue for investigation purposes.
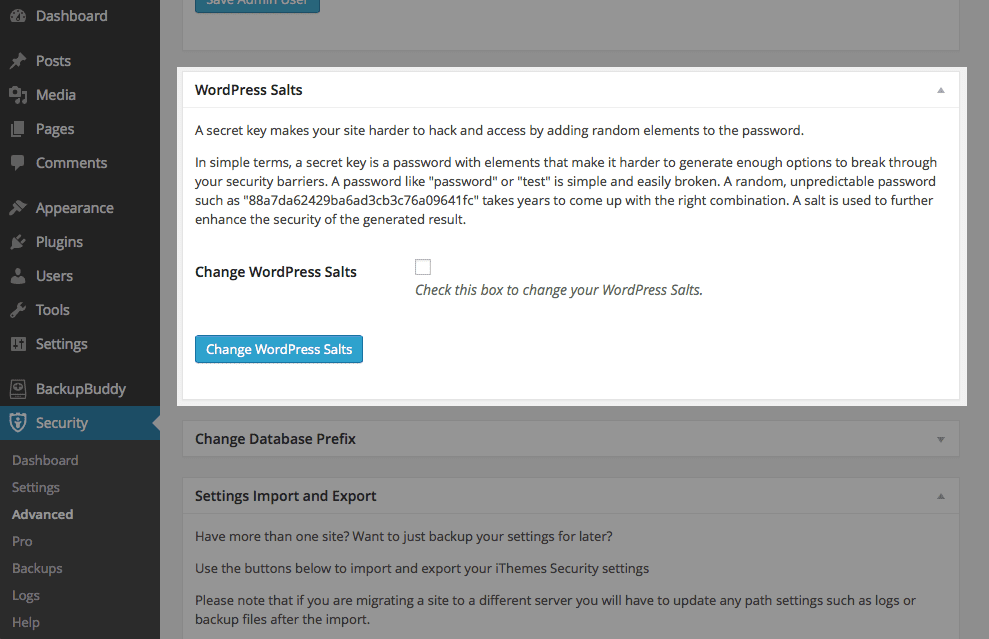
Finally, you must alter every password for accounts and the website. This includes logins for accessing the database, content management accounts, administration, logins for FTP. And ensure that the new passwords aren’t weak.
How Severe is the Attack?
Now, this can vary. You can inspect the hack severity in the Search Console inside the Message Center and Security Issues. And this data or information assists you in comprehending the attack’s severity. All this because cybercriminals can hack your website in plenty of ways.
I mention, here, only a few. Some attackers deploy spam contents which diminishes the quality and search rankings. While some attack to diffuse malware into the website. And some hack for phishing purposes. Now, the way you tackle every kind of hacking can differ. And to examine the type of attack, you must check the messages in the Search Console. There you will notice notifications by Google regarding phishing activities or spam.
Assessment of File System Damage
This step demands an enhanced in-depth investigation. The hacker possesses several potentials to harm your site which encompasses modifying existing pages or even enabling backdoors to grant the hacker to re-enter your website. Firstly, you can identify the files created after comparing it to a strong backup you possess of your site.
Then, inspect the server and error logs and the access as well for unusual and suspicious activities. Treat failed login attempts seriously. And be cautious about unknown user accounts and command history too. Hackers alter and change the logs and records in accordance with their purpose. Hence, be alert.
Identify the Susceptibility of your Website
Your website may possess more than one loopholes. And if you detect one, you must not assume and think that you are done. In fact, you must continue the search since the odds are multiple and it depends on the hacker’s sophistication. Malware scanners are, of course, not fully reliable when it comes to identifying vulnerabilities.
However, a vulnerability scanner does the work pretty well. However, there exist certain possible susceptibilities which are weak or reused passwords, malware-infected system, out-of-date software as well as permissive coding practices.
Indulge in Site Maintainence
For your organizational benefits, website maintainence is an essential part. Presenting your website at its best fetches visitors that can turn into customers with proper guidance. However, you must indulge in maintainence and cleaning your site but prior to that, you must follow certain things.
Firstly, you must determine the support sources to assist you while dealing with confidential information loss. If phishers attack, then most likely that they managed to take your data and discreet information. Then, you may require to eliminate the hacker-created new URLs, if any. However, you must be cautious about removing them. Also, be careful and do not eliminate any good and clean pages that the hackers simply damage. Just concentrate on the ones that you do not desire to showcase in search results.
Cleanse your Server
You must begin with restoring the backup files. But, prior to that, you must be absolutely sure that you created the backup before the website hacking incident. Install software updates and this also includes the Operating System as well. Then, study the current software on your server, and check what you can possibly eliminate.
Alter every password to different accounts of your website. However, you may not be with a backup, which is a common mistake, but it is alright. Now, you must take steps to back them up. Create two backups of your website. Yes, make it even though the website is infected. One performs as a clone model of your website which assists you in restoring content. Whereas, the second counterpart, acts as a file system copy.
After that, you must clean the website’s content that is on the fresh backup file. But, make it absolutely sure that it isn’t the server. Amend any loopholes or vulnerability that you find in passwords. Also, remove widgets, applications or plug-ins which the website requires no long.
However, make sure that whatever you do, is not merely an upgrade but a proper and clean installation. Do not drop files there and bring the untouched or good content to the system from your backup. And finally, change passwords and make them strong. Once you get your site back, you must maintain its security. Hence, you must ensure absolute protection which the remaining article discusses.
Tips to Shield your Website from Hackers
Since every website is vulnerable to attacks, you must refer to certain methods and procedures to protect your site from cybercrime. And such procedures can be a bit complex but with careful adherence to the steps, you will succeed in protecting your website data safe.
Updated Software
You must keep every software on your device up to the date. Be it the Operating System, anti-malware, website security or any other application. You must upgrade them all since they can, in the future, create conflict and provide loopholes for the cybercriminals. Even the hosting services provider you choose must update their software. And for that, you must pick the one which holds a polished reputation in rendering security effectively.
Protection Against Cross-Site Scripting Attacks (XSS)
The hackers have the skill and art to insert malicious JavaScript into the webpage. This, in turn, alters the content. Also, when users and visitors attempt accessing your site, the fail since their credentials along with their cookie details are stolen. Hence, you must look out and monitor if any javascript is present or not.
SQL Injection Attacks
You must incorporate parameterized inquiries as well as abstain from standard Transact SQL. That is because it can potentially offer the hackers to inject rogue code.
Double Validation
I always suggest performing both server-side as well as browser validation. This two-level verification procedure assists you to block such insertion of bad and dangerous scripts via data accepting fields of forms.
File Upload Policy
According to your organizational demands, you will require to offer website visitors the ability to upload images or files to the web server. Also, the cybercriminals or hackers have the skill to compromise your website by releasing dangerous or malicious content.
So, the image, that you view, could possibly be spam in reality. Hence, you must grant file uploads only with severe caution. Also, you must eliminate executable permissions for the file just to avoid execution. This convinces you and ensures website security.
Employ a Hosting Service
You must host your website with a hosting provider. This liberates you from most website security risk responsibility. This is because they look after and take care of the webserver’s website security.
Password Policy
You can implement severe password policies as well as ensure that they are obeyed. Educate and inform the visitors and users on the significance of powerful passwords. Make it mandatory for the users to adhere to the password format that should be of, at least, 8 characters long.
Also, make sure to employ both upper as well as lower case alphabets. Further, instruct them to add symbols or special characters as well. And instruct to avoid dictionary words. Therefore, the longer the passkey involving every must-haves, the stronger the password.
Ensure HTTPs Security
This is an integral portion for security purposes and requires you to inspect if you are on a safe and secure platform. Always check if your website possesses the HTTPs. And this confirms that visitors do not indulge in communication with servers that are essentially fraudulent.
I hope you this article reaches you and guides you efficiently to retrieve your website hack.